Article
Programming Techniques for Considering m Desired Conditions from n Possible Conditions

This work is licensed under a Creative Commons Attribution 4.0 International License.
Copyright
The authors shall retain the copyright of their work but allow the Publisher to publish, copy, distribute, and convey the work.
License
Digital Technologies Research and Applications (DTRA) publishes accepted manuscripts under Creative Commons Attribution 4.0 International (CC BY 4.0). Authors who submit their papers for publication by DTRA agree to have the CC BY 4.0 license applied to their work, and that anyone is allowed to reuse the article or part of it free of charge for any purpose, including commercial use. As long as the author and original source are properly cited, anyone may copy, redistribute, reuse, and transform the content.
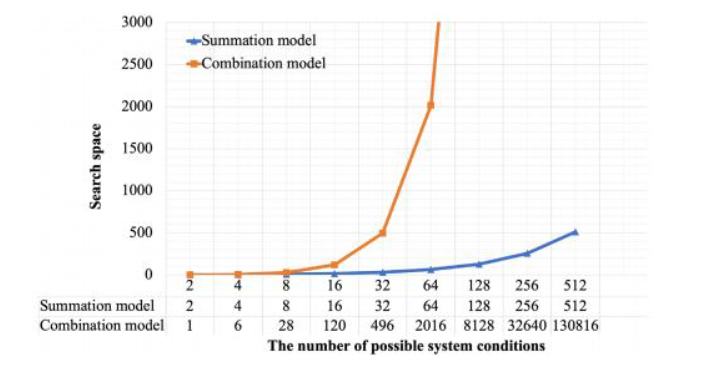
The performance of computer programs (or the hardware that can be programmed such as IoTs, embedded computers, and PLCs) is generally based on the complexity of the particular program development technique. High complexity often uses more execution times and system resources. For this reason, the computer program is less computational complexity to be desired. The conditional statements tell computers what certain information is a major cause of computer program complexities, e.g., considering m desired conditions from n possible conditions. To achieve this aim in computer programs, the data combination is often utilized. However, it is high complexity. Moreover, they cannot give that one condition takes precedence over others. To rid these vulnerabilities of combined conditions, a simple programming technique for considering m desired conditions from n possible conditions is proposed in this work, which is based on the summation of the condition weights. It only has the complexity of search spaces and data constructions to be O(n) and each condition can be set to be different precedence from the others. Furthermore, the proposed technique is evaluated by extensive experiments. From the experimental results, they indicate that the proposed technique is more effective and efficient than the comparative technique.
Keywords:
Condition weights Weighted summations Data combinations Data considerations Programming techniquesReferences
- Chentsov, A., 2017. The program iteration method in a game problem of guidance. Proceedings of the Steklov Institute of Mathematics. 297(1), 43-61.
- Heule, M.J., Kullmann, O., 2017. The science of brute force. Communications of the ACM. 60(8), 70- 79.
- Itai, A., 2001. Generating permutations and combinations in lexicographical order. Journal of the Brazilian Computer Society. 7(3), 65-68.
- Shen, M.K., 1962. On the generation of permutations and combinations. BIT Numerical Mathematics. 2(4), 228-231.
- Karp, R.M., 1975. On the computational complexity of combinatorial problems. Networks. 5(1), 45-68. DOI: https://doi.org/10.1002/net.1975.5.1.45
- Laghari, A., Wu, K., Laghari, R., et al., 2021. A review and state of art of Internet of Things (IoT). Archives of Computational Methods in Engineering. DOI: https://doi.org/10.1007/s11831-021-09622-6
- Suresh, P., Daniel, J.V., Parthasarathy, V., et al., 2014. A state of the art review on the Internet of Things (IoT) history, technology and fields of deployment. 2014 International Conference on Science Engineering and Management Research (ICSEMR). pp. 1-8. DOI: https://doi.org/10.1109/ICSEMR.2014.7043637
- De Silva, L.C., Morikawa, C., Petra, I.M., 2012. State of the art of smart homes. Engineering Applications of Artificial Intelligence. 25(7), 1313-1321. Advanced issues in Artificial Intelligence and Pattern Recognition for Intelligent Surveillance System in Smart Home Environment. DOI: https://doi.org/10.1016/j.engappai.2012.05.002
- Papagiannidis, S., Marikyan, D., 2020. Smart offices: A productivity and well-being perspective. International Journal of Information Management. 51(C). DOI: https://doi.org/10.1016/j.ijinfomgt.2019.10.012
- Deng, T., Kanthawala, S., Meng, J., et al., 2019. Measuring smartphone usage and task switching with log tracking and self-reports. Mobile Media & Communication. 7(1), 3-23. DOI: https://doi.org/10.1177/2050157918761491
- Wilmer, H.H., Sherman, L.E., Chein, J.M., 2017. Smartphones and cognition: A review of research exploring the links between mobile technology habits and cognitive functioning. Frontiers in Psychology. 8. DOI: https://doi.org/10.3389/fpsyg.2017.00605
- Al-Maroof, R.S., Alhumaid, K., Alhamad, A.Q., et al., 2021. User acceptance of smart watch for medical purposes: An empirical study. Future Internet. 13(5). DOI: https://doi.org/10.3390/fi13050127
- Niknejad, N., Ismail, W.B., Mardani, A., et al., 2020. A comprehensive overview of smart wearables: The state of the art literature, recent advances, and future challenges. Engineering Applications of Artificial Intelligence. 90, 103529. DOI: https://doi.org/10.1016/j.engappai.2020.103529
- Shore, J., Warden, S., 2021. The art of agile development. O’Reilly Media, Inc.
- Rigby, D.K., Sutherland, J., Noble, A., 2018. Agile at scale. Harvard Business Review. 96(3), 88-96.
- Abrahamsson, P., Salo, O., Ronkainen, J., et al., 2017. Agile software development methods: Review and analysis. DOI: https://doi.org/10.48550/ARXIV.1709.08439
- Abrahamsson, P., Warsta, J., Siponen, M., et al., 2003. New directions on agile methods: a comparative analysis. 25th International Conference on Software Engineering. Proceedings. pp. 244-254. DOI: https://doi.org/10.1109/ICSE.2003.1201204
- Streule, T., Miserini, N., Bartlom ́e, O., et al., 2016. Implementation of scrum in the construction industry. Procedia Engineering. Selected papers from Creative Construction Conference 2016. 164, 269-276. DOI: https://doi.org/10.1016/j.proeng.2016.11.619
- Sharma, S., Hasteer, N., 2016. A comprehensive study on state of scrum development. 2016 International Conference on Computing, Communication and Automation (ICCCA). pp. 867-872. DOI: https://doi.org/10.1109/CCAA.2016.7813837
- Kniberg, H., 2015. Scrum and XP from the Trenches. Lulu. com.
- Chari, K., Agrawal, M., 2018. Impact of incorrect and new requirements on waterfall software project outcomes. Empirical Software Engineering. 23(1), 165-185.
- Bassil, Y., 2012. A simulation model for the waterfall software development life cycle. DOI: https://doi.org/10.48550/ARXIV.1205.6904
- Chrismanto, A.R., Santoso, H., Wibowo, A., et al., 2019. Developing agriculture land mapping using rapid application development (rad): A case study from Indonesia. International Journal of Advanced Computer Science and Applications (IJACSA). 10(10).
- Martin, J., 1991. Rapid application development. Macmillan Publishing Co., Inc.
- Budoya, C., Kissaka, M., Mtebe, J., 2019. Instructional design enabled agile method using addie model and feature driven development method. International Journal of Education and Development using ICT. 15(1).
- Nawaz, Z., Aftab, S., Anwer, F., 2017. Simplified fdd process model. International Journal of Modern Education & Computer Science. 9(9).
- Amoroso, E., 2018. Recent progress in software security. IEEE Software. 35(2), 11-13.
- Barnum, S., McGraw, G., 2005. Knowledge for software security. IEEE Security & Privacy. 3(2), 74-78.
- McGraw, G., 2004. Software security. IEEE Security & Privacy. 2(2), 80-83.
- Riyana, S., Riyana, N., Nanthachumphu, S., 2017. Enhanced (k, e)-anonymous for categorical data. Proceedings of the 6th International Conference on Software and Computer Applications. pp. 62-67.
- Riyana, S., Nanthachumphu, S., Riyana, N., 2020. Achieving privacy preservation constraints in missing-value datasets. SN Computer Science. 1(4), 1-10.
- Riyana, S., 2021. (lp1,. . . ,lpn)-privacy: privacy preservation models for numerical quasi-identifiers and multiple sensitive attributes. Journal of Ambient Intelligence and Humanized Computing. pp. 1-17.
- Riyana, N., Riyana, S., Nanthachumphu, S., et al., 2020. Privacy violation issues in re-publication of modification datasets. International Conference on Intelligent Computing & Optimization. pp. 938-953. Springer, Cham.
- Riyana, S., Riyana, N., 2021. A privacy preservation model for rfid data collections is highly secure and more efficient than lkc-privacy. The 12th International Conference on Advances in Information Technology. pp. 1-11.
- Duran, R., Sorva, J., Leite, S., 2018. Towards an analysis of program complexity from a cognitive perspective. Proceedings of the 2018 ACM Conference on International Computing Education Research, ICER. Association for Computing Machinery, New York, NY, USA. 18, 21-30. DOI: https://doi.org/10.1145/3230977.3230986
- Wolf-Branigin, M., 2013. Using complexity theory for research and program evaluation. Oxford University Press.
- Daly, D., Brown, W., Ingo, H., et al., 2020. The use of change point detection to identify software performance regressions in a continuous integration system. ICPE. Association for Computing Machinery, New York, NY, USA. 20, 67-75. DOI: https://doi.org/10.1145/3358960.3375791
- Aleti, A., Trubiani, C., van Hoorn, A., et al., 2018. An efficient method for uncertainty propagation in robust software performance estimation. Journal of Systems and Software. 138, 222-235. DOI: https://doi.org/10.1016/j.jss.2018.01.010
- Grechanik, M., Luo, Q., Poshyvanyk, D., et al., 2016. Enhancing rules for cloud resource provisioning via learned software performance models. ICPE. Association for Computing Machinery, New York, NY, USA. 16, 209-214. DOI: https://doi.org/10.1145/2851553.2851568
- Catuogno, L., Galdi, C., Pasquino, N., 2018. An effective methodology for measuring software resource usage. IEEE Transactions on Instrumentation and Measurement. 67(10), 2487-2494. DOI: https://doi.org/10.1109/TIM.2018.2815431

 Download
Download